12.16.198.1100: System Traffic Analysis
The IP address 12.16.198.1100 serves as a critical node for analyzing system traffic. Understanding its behavior can reveal significant trends in network usage and potential vulnerabilities. Various tools and methodologies are employed to dissect this traffic, offering insights into both security and performance. The implications of these findings extend beyond mere observation, prompting a need for strategic action. What specific challenges and solutions emerge from this analysis?
Understanding Traffic Patterns of IP 12.16.198.1100
How can the traffic patterns of a specific IP address, such as 12.16.198.1100, provide insights into network behavior?
By analyzing traffic behavior, one can identify usage trends, potential security threats, and performance bottlenecks.
Employing data visualization techniques facilitates the interpretation of complex datasets, revealing patterns that inform decision-making.
Understanding these dynamics empowers users to optimize network efficiency and enhance overall freedom of operation.
Tools and Methodologies for Traffic Analysis
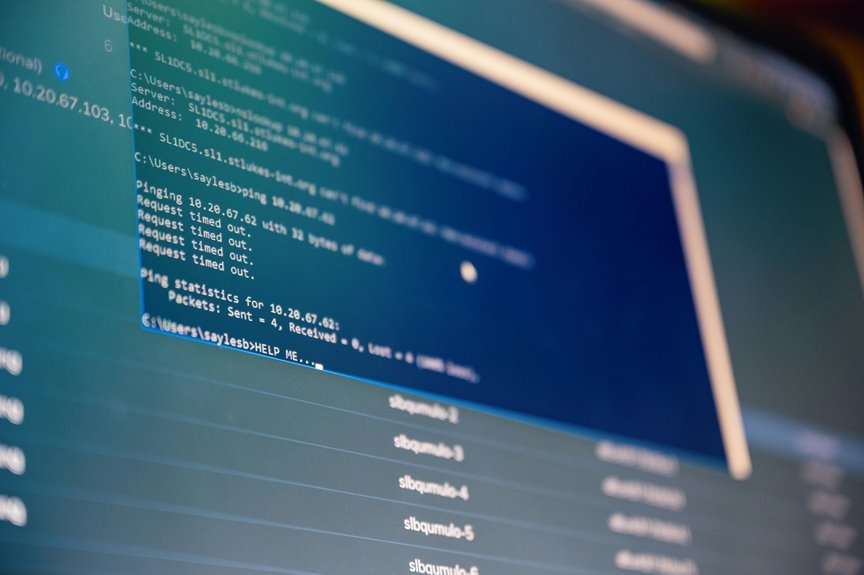
While the selection of appropriate tools and methodologies is crucial for effective traffic analysis, various options exist to suit different network environments and objectives.
Packet capture tools enable the collection of network data, while protocol analysis software facilitates the examination of communication patterns.
Employing both approaches enhances the understanding of traffic flows and optimizes network performance, allowing for informed decision-making in network management.
Implications for Network Security and Performance
The effectiveness of traffic analysis tools and methodologies directly influences network security and performance.
Accurate threat detection enhances the ability to identify vulnerabilities and mitigate risks, fostering a secure environment.
Simultaneously, performance optimization ensures that network resources are utilized efficiently, preventing bottlenecks and maintaining user satisfaction.
Ultimately, a balanced approach to both aspects is essential for sustaining robust networking capabilities in a dynamic landscape.
Conclusion
In the grand circus of network management, IP address 12.16.198.1100 takes center stage, dazzling analysts with its intricate traffic patterns. Armed with packet capture tools, these modern-day wizards conjure insights that are as enlightening as they are alarming. Yet, amidst the acrobatics of performance optimization and security vigilance, one must wonder: will the network ever learn to juggle its resources without dropping the ball? Only time will reveal whether this digital tightrope act ends in applause or catastrophe.